Why is jailbreak detection important? – COVID apps case
There are many applications/tweaks allowing changing your GPS coordinates on iOS. Detection of those is however not simple. There are a few approaches like constantly reporting the user’s location or analyzing the user’s velocity.

Some time ago I got stuck in the USA because of the COVID-19. After coming back to Poland with the “evacuation flight” I had to undergo mandatory quarantine for 14 days. Every day the Polish Police was visiting me and checking if I’m sitting at home and don’t go outside. As we all expected it was a big overhead to the Police since they had to visit every day each quarantined person. My friends told me that I can install an official government app that reports my location everyday. After the installation, the user has to complete an everyday task that includes sending a selfie from home. Under the hood, the application also reports the user’s location. I started considering if the application is properly protected against the GPS spoofing attacks.
Use the force hyperdrive
There are many applications/tweaks allowing changing your GPS coordinates on iOS. Detection of those is however not simple. There are a few approaches like constantly reporting the user’s location or analyzing the user’s velocity. The quarantine application I installed didn’t support such mechanisms (actually I saw an anti GPS spoofing method in the code but it was probably only a mock). So, I jailbroken my iPhone, downloaded the AkLocationX tweak and opened the quarantine application. After successful registration I spoofed my location as follows:
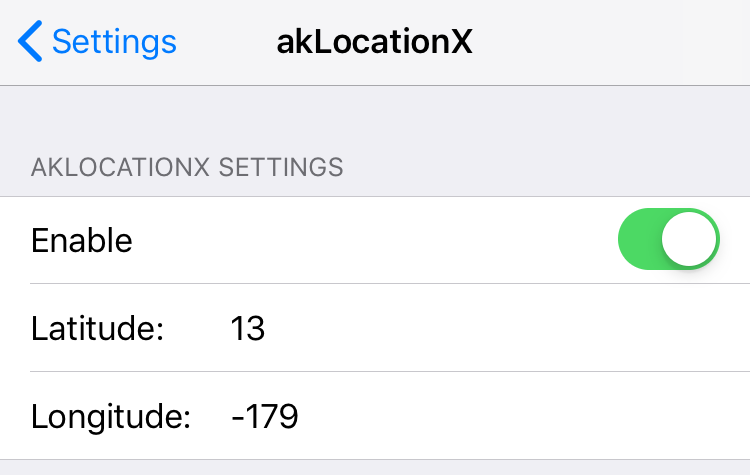
Opened the application and it turned out I was on somewhere in the North Pacific Ocean.

As you can see, tricking this application was rather simple, and a script-kiddie can bypass the quarantine. That may influence social health. In the next section, I’ll show you an improvement that can help with detecting such suspicious behaviors.
Jailbreak detection
As Wikipedia says:
Jailbreaking is the privilege escalation of an Apple device for the purpose of removing software restrictions imposed by Apple on iOS, iPadOS, tvOS, and watchOS operating systems. This is typically done by using a series of kernel patches. Jailbreaking permits root access in Apple’s mobile operating system, allowing the installation of software that is unavailable through the official Apple App Store.
To trick the quarantine application I had to have a jailbroken device first. It was required to install the GPS spoofing tweak. So, the idea is to detect that jailbreak and appropriately respond. For the quarantine applications maybe it’s a good solution no to trust the GPS localization on jailbroken devices and send Police to verify the user’s location?
Freedom vs jailbreaking
Here, I need to say I’m totally against blocking applications on devices where the jailbreak is detected. Users should have a choice to use jailbroken or jailed device. However, I also understand the fact that jailbroken devices tend to be less secure. Jailbreaking usually means staying on an outdated iOS version with known vulnerabilities, sometimes killing or modifying important security daemons. I remember the times where the SSH server was bound to all interfaces with the root:alpine credentials. So if you had connected to a public WiFi without device isolation any person would have been able to take over your device and execute any command as root.
We need to reach a compromise. High-risk applications have to somehow respond when they are run on the modified environment. In my opinion, the good solution is to perform the jailbreak checks, log it, inform the user that their device is jailbroken and they accept the risk using such a device.
Jailbreak detection cannot be fully trusted
Jailbreak detection is performed on the device which can be fully controlled by the user. It means that the attacker will always win! If the attacker has root permissions and can modify everything on the device they can also write an anti-anti-jailbreak mechanism. It can be done by modifying the application, creating a special tweak, running a Frida script or even creating a kernel extension.
You should always treat jailbreak detection as of another layer of security. It is really important to understand that implementing a jailbreak detection cannot be your only defense. The applications always have to be coded securely, doesn’t matter if the device is jailbroken or not.
Other COVID applications
In this research, I also quickly looked on some other quarantine applications. While I didn’t have access to the activated versions I just performed quick static and semi-dynamic analysis to see if the apps detect jailbreaks. It turned out that only 1 of 5 applications I quickly analyzed had such “protection”.
Summary
The Polish quarantine application on iOS was easily bypassable which could have had an influence on public health. The application had no GPS spoofing protection nor the jailbreak detection mechanisms. When jailbreak detection is not usually important and required there are some types of applications that it should be implemented. Even one, simple security layer may stop the “script kiddies” from bypassing the crucial features. On the other hand, we have to remember that the experienced attacker will always win when the checks are performed on the device. Do not do the false assumptions and always make sure your application is coded securely.
If you want to implement a jailbreak detection mechanism in your application take a look at our free & open source library – iOS Security Suite. You can find it on the Github – https://github.com/securing/IOSSecuritySuite
Head of Mobile Security



