Mac Environment Security

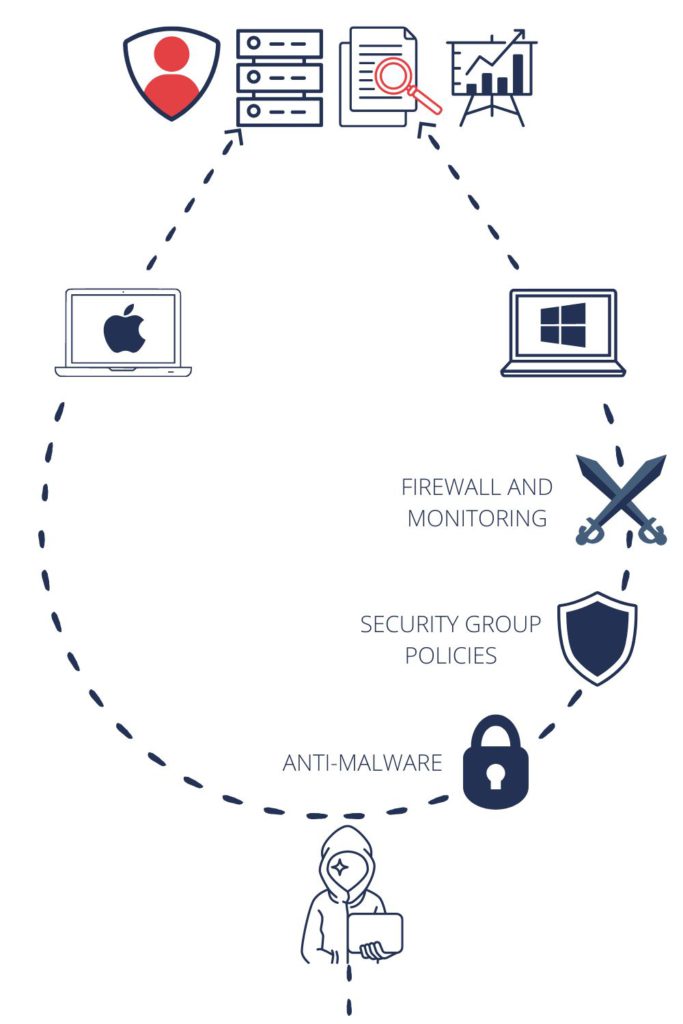
The security of each IT infrastructure is the sum of the security features of all its components. If you have different operating systems inside your organization, it is worth ensuring the standardization of their security.
What do we check?
We are experienced in testing environments based on various management systems, including:
- JAMF Pro,
- Apple Business Manager (MDM),
- VMWare Workspace ONE,
- Scalefusion MDM,
- SimpleMDM,
- Cisco Meraki,
- Miradore MDM.
During tests, we focus on the comprehensive analysis of an architecture, configuration of each workstation, and the work style specific to each organization. This holistic approach makes it possible to understand where the weaknesses of an organization really lie.
Adding computers with macOS often means adding other Apple devices as well. So, if your environment includes iPhones, iPads, AppleTVs, and other iDevices, we will also help you verify their security.
As your organization grows, the number of devices with access to the company’s key resources expands. Therefore, it is worth considering the appropriate planning for granting access.
What does a Mac infrastructure test look like?
From the very beginning, we focus on close collaboration for the best coverage of your infrastructure. Each infrastructure is slightly different from the others, but usually, we are distinguishing 6 stages in our workflow:
STEP 1: Defining the scope of the environment security test and signing the contract.
STEP 2: We organize an opening meeting during which, together with administrators and architects, we discuss how an infrastructure architecture was designed. At such a meeting, we also specify the iDevices used in the company.
STEP 3: We conduct threat modeling to identify potential targets of the attacker and those who might want to harm the organization.
STEP 4: Security test – the main stage of our cooperation. We look closely at the aspects such as account management panels, workstations, and connections between them. All findings are thoroughly presented in the form of a report.
STEP 5: Wrap-up meeting – we will go through the report and answer any questions related to the removal of vulnerabilities.
STEP 6: After each security test, we suggest verifying the effectiveness of the vulnerability removal.
The result of a review
A summary report includes a list of vulnerable spots and recommendations based on the best security practices.
Each service we provide is based on our own research. Our team includes people who specialize in security of Apple devices. One example of such research is the presentation “Abusing & Securing XPC in macOS apps” by Wojciech Reguła. The presentation took place at a leading conference about iDevices security in the United States.
DORA compliance
Mac Environment Security Testing can contribute to the compliance with DORA principles. It aligns with DORA’s comprehensive security view.
How to get a quote for your project?
If you are interested in Mac environment security tests in your organisation or need assistance with verifying common threats, book a discovery call or just leave us a message.




