Threat Modeling session on demand
What is threat modeling?
It is like a penetration test but done “on a piece of paper”. For a new system, it helps produce a list of security requirements. For an existing system, it helps provide a comprehensive list of potential attack scenarios and verify which of them pose a real threat.
Our TM is a one-time session with our IT security experts, during which we will identify critical threats to your application, system, infrastructure, or physical office security. You will get a detailed report verified by our experts, including recommendations for implementing specific security measures.
What does the session look like?
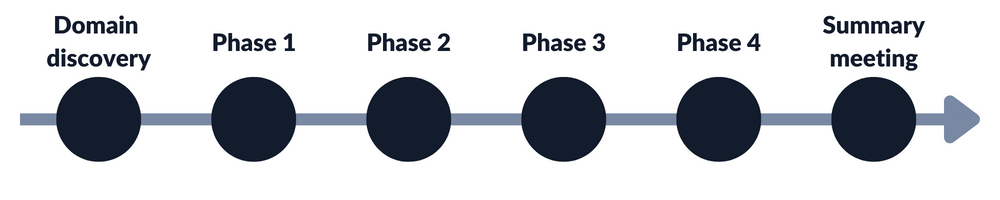
Domain discovery
We start with a short discussion about the subject of the TM both from a business and a technical angle. This is a domain discovery process and resource gathering. The main goal of this step is to understand your solution/system and the environment in which it operates.
You can expect a lot of questions from us, but do not worry – we will send you helpful preparation materials in advance.
Phase 1 – “Who?”
During the first stage, we will identify potential threat actors in the system. Who could attack your system, or precisely, what are their initial roles? E.g., an unauthorized Internet user, an attacker registered as an application user, or an attacker who managed to gain rights of an administrator.
Phase 2 – “What?”
The next step is identifying your critical assets and potential goals of the attacker. What can go wrong? What is your worst nightmare when it comes to your organization? What do you fear the most? What would an attacker want to achieve? What is crucial from the business perspective? Because disruptive thinking is not typically practiced by development teams, we will start with some simple exercises to help you understand the attacker’s perspective.
Phase 3 – “How?”
After identifying potential attackers (Who?) and potential goals (What?), we will use our expertise and experience to think about How attackers may achieve their goals. At the end of this phase, you will get a list of threats that you should always keep in mind.
Phase 4 – Remediations
Making the list of priorities and selecting the most important threats. After our internal analysis, we will propose a range of possible solutions to the threats found.
Reporting & Summary meeting
After the workshop, we will create a document summarizing the whole threat modeling session.
Our summary will be divided into three parts:
- Threats (What can an attacker do?)
- Exemplary attack vectors (How can an attacker achieve the given goal?)
- Security requirements (Countermeasures to prevent the given attack).
Next, we will arrange a short summary meeting, during which we will go through the document.
Who is threat modeling for?
Thanks to threat modeling, you can take a broad look at your entire organization. This way, we can effectively influence essential aspects and employees’ attitude towards security. Here is how your organization will benefit from a threat modeling session:
Business – benefits from better transfer and promotion of knowledge about cybersecurity. Important security decisions will be made at a very early stage, saving you money for making future improvements. We help building clear procedures to improve organization’s functioning.
Team leader and Project management – threat modeling significantly reduces the project implementation time – instead of fixing security issues, we focus on predicting and preventing them and creating solutions that are safe by default. This way, we develop competences of your team, nurturing the continuity of software delivery in different models (Waterfall, Agile, CI/CD).
Security team – threat modeling process creates scenarios that might be used further in the security testing phase. Actually, our pentesting team is using TM every day during the test preparation phase to create attack ideas. Thanks to the fact that many people working in your company will be involved in the TM session, they will become more aware of the security issues and your whole organization will become safer.
Developers and Architects – it is essential to not only have a broad perspective, but also to implement it into everyday work. It is the production team that threat modeling has the biggest impact on. Take a step forward and develop solutions that are secure by default.
DORA compliance
Threat Modeling session on demand can contribute to the compliance with DORA principles. It aligns with DORA’s emphasis on proactive security measures.
Interested? – Let’s talk about your case
Fill out our contact form, indicating that you are interested in threat modeling. We will get back to you soon with our full offer.
You can also schedule a short discovery call straight away by selecting a time slot in the calendar below:
Articles on Threat Modeling
In the meantime, we recommend you articles on threat modeling from our Knowledge Base:




